How to browse DarkWeb using .NET 6

Threat Intelligence is a crucial part of Cyber Security domain and most of the threat actors hang out on the DarkWeb. This makes it interesting to mine data from DarkWeb and analyse it. Its useful to gain insight and also to extract relevant data to make predictions for the future.
There has been several projects on how to reach DarkWeb and consume the information. In this article we look at how its done using the latest .NET 6 Socks support.
What is Tor?
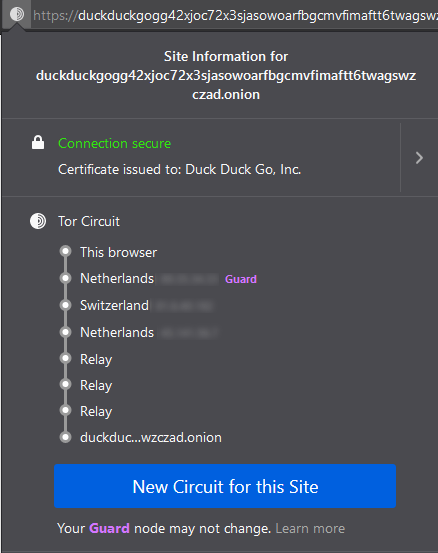
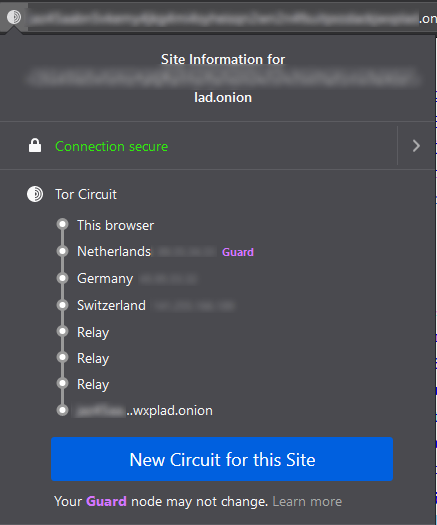
Tor is a program you can run on your computer that helps to keep you safe on the Internet. It protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world. Also prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location. This set of volunteer relays is called the Tor network.
The Tor Project is a non-profit (charity) organization that maintains and develops the Tor software.
The next important component of Tor is called Tor Browser which is used commonly to browse DarkWeb. Its is a modified version of Firefox with some additions specific to support Tor Network.
Websites on DarkWeb uses .onion domain name and are not accessible from the Open Web unless you go through Tor.
How does the Tor Relay bouncing looks like?
What is SOCKS ?
Socket Secure or in short SOCKS is an Internet Protocol that exchanges network packets between a client and server through a proxy server. SOCKS5 additionally provides authentication so only authorized users may access a server. A SOCKS server proxies TCP connections to an IP address, and provides a means for UDP packets to be forwarded.
SOCKS runs at Layer 5 of the OSI model (the session layer) between transport and presentation layer. In the case of Tor browser, Tor component (tor.exe in Windows) listens on localhost (127.0.0.1) port 9050 by default and acts as a SOCKS proxy for the Tor Browser.
SOCKS proxy is not the same as HTTP proxy
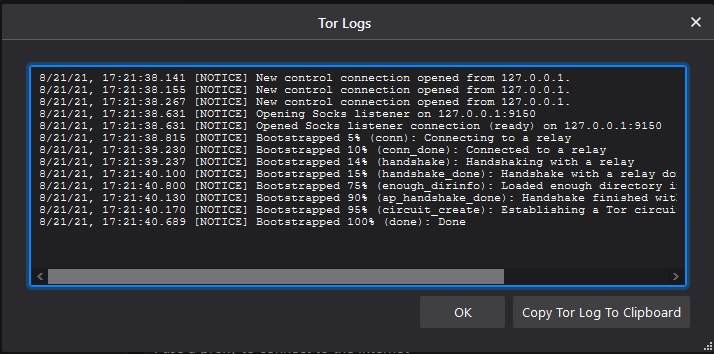
When Tor Browser is used, behind the scene it setup Tor.exe as a socks proxy to listen on localhost port 9150.
You can view this from Tor Browser > Settings > Tor > View Logs…
SOCKS have had different versions SOCKS4, SOCKS4a (added domain name support) and now SOCKS5 (added authentication support). RFC links at the bottom of this article under resources.
The key improvements in SOCKS version 6 (currently in draft) over SOCKS version 5 are:
- The client sends as much information upfront as possible, and does not wait for the authentication process to conclude before requesting the creation of a socket.
- The connection request also mimics the semantics of TCP Fast Open [RFC7413]. As part of the connection request, the client can supply the payload for the initial SYN that is sent out to the server.
- The protocol can be extended via options without breaking backward-compatibility.
- The protocol can leverage the aforementioned options to support 0-RTT authentication schemes.
How does it work?
Keep in mind, Tor project website is going through a change at the moment so links are not easy to find.
When Tor.exe is run, it acts as a SOCK proxy listening on localhost port 9050. Our application then connects to this listening endpoint and rest is taken care of by Tor networks magic.
To use Tor in our own application on Windows we need to download something called Windows Expert Bundle. This contains the binary to run the SOCKS proxy.
Click here for the download page. It comes as a zip file and you need to extract it on your file system.
The zip file once extracted contains 2 folders. One called Tor and other one called Data. Tor folder contains the binaries and the Data folder contains 2 files with the names geoip (for IPv4) and geoip6 (IPv6). These files contains IP addresses which are mapped to the country it belongs to. By default its not used but it can be configured if required.
Tor.exe is the SOCKS proxy listener which when executed runs on localhost port 9050 by default.
Tor.exe uses a configuration file called “torrc“. Default location for this file on Windows is “C:\Users\<user>\AppData\Roaming\tor\”. In case you don’t find, you can get a sample from Tor unofficial Github page. Or create one yourself in the same folder as Tor.exe and pass it as a parameter (Tor -f torrc)
You can find below, some useful configurations to include in the torrc config file. Just create a file called torrc in notepad and add these. Lines starting with ‘#’ is considered as comment.
## Configure GeoIPFiles
GeoIPFile D:\tor\Data\Tor\geoip
GeoIPv6File D:\tor\Data\Tor\geoip6
## SOCK proxy listener configuration - default => localhost:9050
#SOCKSPort 9050 # Default: Bind to localhost:9050 for local connections.
#SOCKSPort 192.168.0.1:9100 # Bind to this address:port too.
## Send all messages of level 'notice'
#Log notice file D:\tor\logs\notices.log
## Send every possible message => this has lot of info only for debug
#Log debug file D:\tor\logs\debug.log
If you try running Tor.exe without config file, the output looks like below. ‘Done’ at the end means SOCKS proxy is ready for use.
> tor
[datetime] [notice] Tor 0.4.5.9 (git-d0ed04d50e80fe1c) running on Windows 8 [or later] with Libevent 2.1.12-stable, OpenSSL 1.1.1k, Zlib 1.2.11, Liblzma N/A, Libzstd N/A and Unknown N/A as libc.
[datetime] [notice] Tor can't help you if you use it wrong! Learn how to be safe at https://www.torproject.org/download/download#warning
[datetime] [notice] Configuration file "C:\Users\<user>\AppData\Roaming\tor\torrc" not present, using reasonable defaults.
[datetime] [notice] Opening Socks listener on 127.0.0.1:9050
[datetime] [notice] Opened Socks listener connection (ready) on 127.0.0.1:9050
[datetime] [notice] Parsing GEOIP IPv4 file D:\tor\Data\Tor\geoip.
[datetime] [notice] Parsing GEOIP IPv6 file D:\tor\Data\Tor\geoip6.
[datetime] [notice] Bootstrapped 0% (starting): Starting
[datetime] [notice] Starting with guard context "default"
[datetime] [notice] Bootstrapped 5% (conn): Connecting to a relay
[datetime] [notice] Bootstrapped 10% (conn_done): Connected to a relay
[datetime] [notice] Bootstrapped 14% (handshake): Handshaking with a relay
[datetime] [notice] Bootstrapped 15% (handshake_done): Handshake with a relay done
[datetime] [notice] Bootstrapped 75% (enough_dirinfo): Loaded enough directory info to build circuits
[datetime] [notice] Bootstrapped 90% (ap_handshake_done): Handshake finished with a relay to build circuits
[datetime] [notice] Bootstrapped 95% (circuit_create): Establishing a Tor circuit
[datetime] [notice] Bootstrapped 100% (done): DoneKeep in mind, if the configuration file is provided then the output will be truncated and only shows like below. I wasted quite sometime troubleshooting.
> tor -f torrc
[datetime] [notice] Tor 0.4.5.9 (git-d0ed04d50e80fe1c) running on Windows 8 [or later] with Libevent 2.1.12-stable, OpenSSL 1.1.1k, Zlib 1.2.11, Liblzma N/A, Libzstd N/A and Unknown N/A as libc.
[datetime] [notice] Tor can't help you if you use it wrong! Learn how to be safe at https://www.torproject.org/download/download#warning
[datetime] [notice] Read configuration file "D:\tor\Tor\torrc".
[datetime] [notice] Opening Socks listener on 127.0.0.1:9050
[datetime] [notice] Opened Socks listener connection (ready) on 127.0.0.1:9050We have SOCKS proxy listening, now what?
This is where the fun part is, .NET 6 Preview 5 introduced support for SOCKS4, SOCKS4a & SOCKS5. The implementation is made so simple that you only need few lines of code to make it work.
Steps below
- Create a console app
- Copy paste the below code snippet in Program.cs
- Compile & Run
> dotnet new console -n torifyLets see those few lines of code to copy paste.
// New minimalistic way of writing C# code in .NET 6
using System.Net;
// DarkWeb DuckDuckGo v3 website url
Uri url = new("https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion");
HttpClient client = new(new HttpClientHandler
{
// Magic happens with socks scheme used below
Proxy = new WebProxy("socks5://127.0.0.1:9050")
});
Console.WriteLine(await client.GetStringAsync(url));
In case you like to download the project and run it, Github Repo is here => Torify.NET
Summary
In this article we saw how to use SOCKS5 support introduced in .NET 6.0 to connect and browse DarkWeb .onion websites.
Resources
- Tor Project website
- Tor Project History
- Tor Browser Download
- SOCKS5 protocol RFC
- SOCKS6 protocol draft RFC

cool
LikeLiked by 1 person